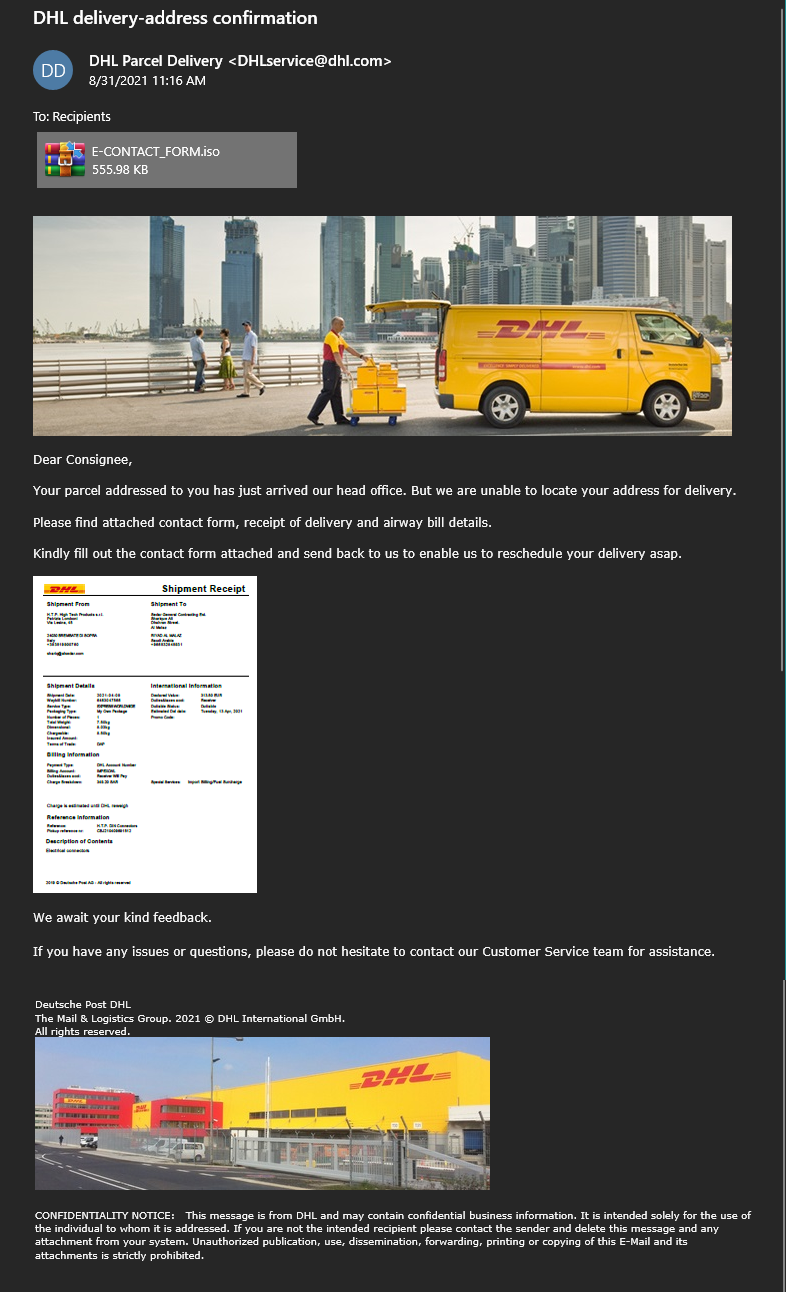
Cryptocurrency Stealer BluStealer Spreads via Fake DHL Malspam Campaign
23 SEP 2021
Avast Threat Labs traced cryptocurrency stealer, keylogger and document uploader that loads hack tools to steal credentials of thousands of users

September 23, 2021
Avast Threat Labs traced cryptocurrency stealer, keylogger and document uploader that loads hack tools to steal credentials of thousands of users
For more information contact us :
E-mail : press@gendigital.com
About Avast
Avast is a leader in digital security and privacy, and part of Gen™ (NASDAQ: GEN), a global company dedicated to powering Digital Freedom with a family of trusted consumer brands. Avast protects hundreds of millions of users from online threats. Its products for Mobile, PC or Mac are top-ranked and certified by VB100, AV-Comparatives, AV-Test, SE Labs and others. Avast is a member of the Coalition Against Stalkerware, No More Ransom and Internet Watch Foundation. Learn more at Avast.com.
Keep in touch with Avast:
- For security and privacy insights, visit the Avast blog: https://blog.avast.com/
- For handy guides, advice and tips, visit Avast Academy: https://www.avast.com/c-academy
- For in-depth technical analysis of online threats, visit the Avast Decoded blog: https://decoded.avast.io/
- For more information about Avast visit: https://www.avast.com/en-gb/about and https://www.avast.com/company-faqs
- Follow us on Twitter: @Avast
- Join our LinkedIn community: https://www.linkedin.com/company/avast
- Visit our Facebook group: www.facebook.com/avast